
WordPress.org Forces Security Update for Critical Ninja Forms Vulnerability
…Full post on WP Tavern
Read Full

…Full post on WP Tavern
Read Full

WooCommerce 7.5.0 was released this week with three new blocks for the Product Archive templates. These include a new Store Breadcrumb block, Product Results Count block, and a Catalog Sorting block, all seen in action below. image credit: WooCommerce 7.5.0 Release Post These blocks were released as part of an effort to “blockify” Product Archive…
Husband-and-wife duo Topher and Cate DeRosia announced the launch of the The HeroPress Network earlier today. It is a collection of content from various sites they are working on in a centralized location. “Its overarching goal is to be a hub,” said Cate DeRosia. “It will display the newest items from around the HeroPress Network,…
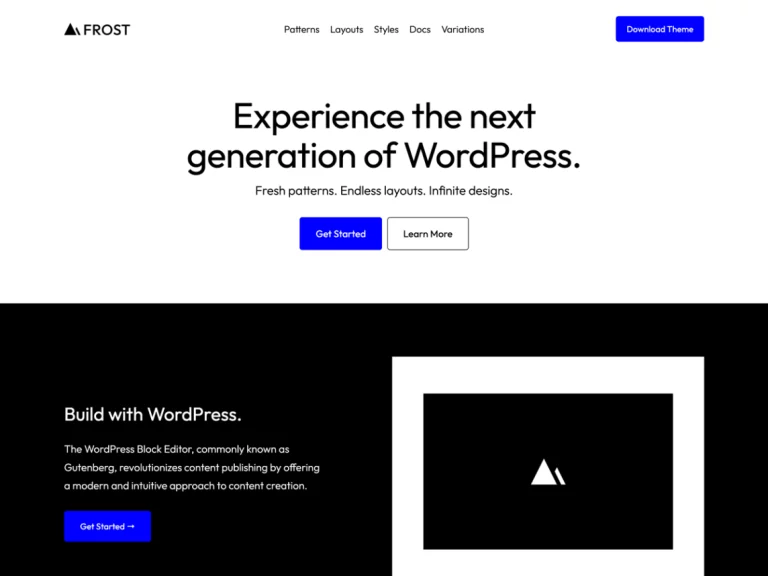
The WordPress Themes Directory is now hosting more than 300 block themes, a milestone for the dedicated theme developers who have persevered through the growing pains and evolution of block theming. WP Engine is one of the newest theme authors who helped put the directory over the 300 mark with its submission of Frost. With…

The WordPress community is ending two days of heated discussions that rapidly descended into a mire of unbridled emotional confrontations across multiple social channels, following a tweet from John Blackbourn that raised concerns about WordPress.com plugin listings outranking WordPress.org on Google Search. Developers expressed concerns about the SEO impact of the practice of cloning WordPress.org’s…
GitHub has announced that Copilot, its new AI pair programming assistant, is now available to developers for $10/month or $100/year. Verified students and maintainers of open source projects will have free access to Copilot. The assistant is available as an extension for popular code editors, including Neovim, JetBrains IDEs, Visual Studio, and Visual Studio Code….
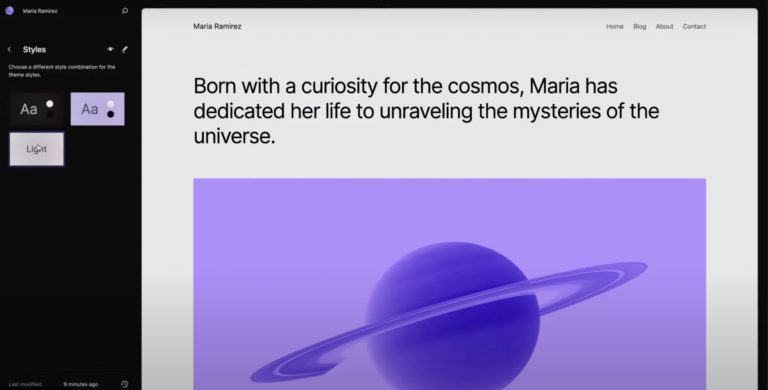
WordPress 6.3 “Lionel” was released earlier this week with an overview video that offers a beautiful, dizzying demo of the many new features packed into this update. It’s a two-minute guided tour of WordPress’ greatly expanded customization features, streamlined Site Editor interface, pattern creation and management, and the new Command Palette in action. For the…